• Tunneling is an internetworking strategy that is used when source and destination networks of same type are connected through a network of different type.
• In such a case, the packet from one network reaches the other network via different kind pf network that interconnects them.
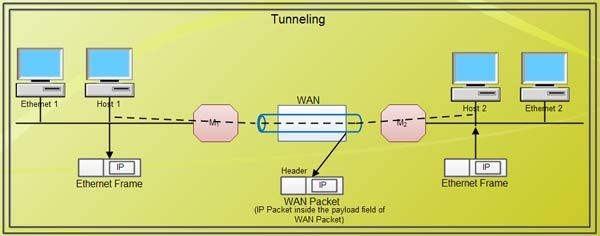
• To understand tunneling, let an Ethernet is to be connected to another Ethernet via a WAN.
• The IP packets are to be sent from host 1 of Ethernet 1 to host 2 of Ethernet 2 via a WAN.
• To send an IP packet to host 2, host 1 constructs the packet containing the IP address of host 2.
• It then inserts this packet into an Ethernet frame. This frame is addressed to the multi-protocol router M1 and is placed on Ethernet.
• When this packet reaches, multiprotocol router MI, it removes the IP packet and insert it in the payload field of the WAN network layer packet.
• This WAN network layer packet is then addressed to multi-protocol router M2.
• When this packet reaches M2, it removes the IP packet and inserts it into the Ethernet frame and sends it to host 2.
• In the above process, IP packets do not have to deal with WAN, they just travel from one end 0f the tunnel to the other end. The host 1 and host 2 on two Ethernet also do not have to deal with WAN.
• The multi-protocol routers M1 & M2 understand about IP and WAN packets.
 Dinesh Thakur holds an B.C.A, MCDBA, MCSD certifications. Dinesh authors the hugely popular
Dinesh Thakur holds an B.C.A, MCDBA, MCSD certifications. Dinesh authors the hugely popular