• Security Hash Algorithm (SHA) was developed in 1993 by the National Institute of Standards and Technology (NIST) and National Security Agency (NSA).
• It was designed as the algorithm to be used for secure hashing in the US Digital Signature Standard.
• Hashing function is one of the most commonly used encryption methods. A hash is a special mathematical function that performs one-way encryption.
• SHA-l is a revised version of SHA designed by NIST and was published as a Federal Information Processing Standard (FIPS).
• Like MD5, SHA-l processes input data in 512-bit blocks.
• SHA-l generates a 160-bit message digest. Whereas MD5 generated message digest of 128 bits.
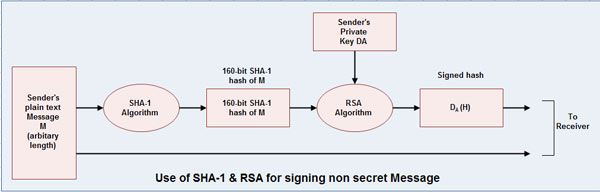
• The procedure is used to send a non secret but signed message from sender to receiver. In such a case following steps are followed:
1. Sender feeds a plaintext message into SHA-l algorithm and obtains a 160-bit SHA-l hash.
2. Sender then signs the hash with his RSA private key and sends both the plaintext message and the signed hash to the receiver.
3. After receiving the message, the receiver computes the SHA-l hash himself and also applies the sender’s public key to the signed hash to obtain the original hash H.
 Dinesh Thakur holds an B.C.A, MCDBA, MCSD certifications. Dinesh authors the hugely popular
Dinesh Thakur holds an B.C.A, MCDBA, MCSD certifications. Dinesh authors the hugely popular