The ring architecture is a distributed architecture, with minimal connectivity and a topology of two links connected to every node as shown in Figure and forms unbroken circular configuration. Figure shows a network laid out in a physical ring, or closed loop, configuration. Transmitted messages travel from node to node around the ring. Each node must be able to recognize its own address in order to accept messages.
Information travels around the ring in only one direction, with each attached station or node serving as, a repeater. Rings generally are coaxial cable or fiber in nature, operating at raw transmission rates of 4, 16, 20 or 100Mbps or more. Rings are deterministic in nature, employing token passing as the method of media access control to ensure the ability of all nodes to access the network within a predetermined time interval.

Ring network with centralized control are known as loops. When ring networks with distributed control are used, some form of control strategies must be used to avoid conflicting demands for the shared channel. The popular control strategies are token passing, circulating slot, register insertion techniques.
Priority access is recognized. A. master control station is responsible for controlling access to the transmission medium. Backup control stations assume responsibility in the event of a failure of the master. Throughput is very close to raw bandwidth, as data collisions do not occur in such a carefully controlled environment. On the negative side, the failure of a single node can compromise the entire network. Ring networks are specified in the IEEE 802.5 standard. Token-Passing Ring, IBM Token Ring, and FDDI all are based on ring topologies.
Examples of Token Ring Topology
IBM Token Ring A local area network access mechanism and topology in which all stations actively attached to the bus listen for a broadcast token or supervisory frame. Stations wishing to transmit must receive the token before doing so. After a station finishes transmission, it passes the token to the next node in the ring. It operates at 16 Mbps and can be used with computers from IBM, computers from other vendors and peripheral devices such as printers.
The IEEE published its standard as IEEE 802.5 for token ring in -1984 after IBM Token Ring specifications. Therefore, the IEEE 802.5 specification is almost identical to, and completely compatible with, IBM Token Ring network. The objective of Token Ring is to provide reliability at all functional levels of LAN. This topology addresses issues like systematic wiring, ease in configuration and maintenance, fault tolerance and redundancy.
FDDI (Fiber Distributed Data Interface)
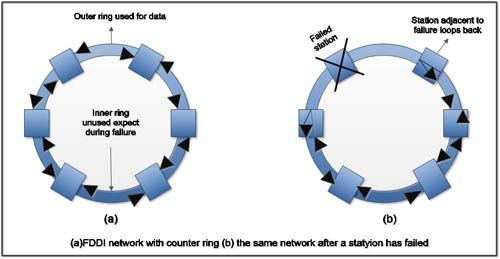
FDDI is a reliable, high-speed network for high traffic. It can transport data at a rate of 100Mbps and can support up to 500 stations on a single network. FDDI was designed to run through fiber cables, transmitting light pulses to convey information back and forth between stations, but it can also run on copper using electrical signals. A related technology, Copper Distributed Data Interface (CDDI) works FDDI using copper cables instead of fiber cables. FDDI maintains a high reliability because FDDI networks consist of two counter-rotating rings as shown in Figure (a).These rings work to back each other up, so should something go wrong on the network, an alternate way to get the data can be found. Figure (b) illustrates the data flow when one station failed. After a station fails, adjacent stations use the reverse path to form a closed ring. FDDI is also considered reliable because it has mechanisms to fix its own problems.
 Dinesh Thakur holds an B.C.A, MCDBA, MCSD certifications. Dinesh authors the hugely popular
Dinesh Thakur holds an B.C.A, MCDBA, MCSD certifications. Dinesh authors the hugely popular