We’ll be covering the following topics in this tutorial:
Multitasking Systems
Most modern operating systems allow running multiple tasks both: a computer can, while executing a user program, read the data from a disk or display results on a terminal or printer. We talk about multi-tasking operating system or multi-programmed in this case.
Process
The fundamental notion of multi-tasking operating systems is the process. the program concept is not enough. Nothing prevents the same program is executed several times simultaneously: one may want, for example, two windows emacs or two gv windows to compare texts.
A process is a program instance being run.
A process is represented by a program (the code), but also its data and by parameters indicating where it is, allowing it to continue if it is interrupted (execution stack, program counter …). We talk about the program environment.
A process is also called task in the case of Linux.
Timeshare
Most multi-tasking operating systems are implemented on a computer having a single microprocessor. This one, at a given moment, really runs one program, but the system can do switch from one program to another by running each program for several tens of milliseconds; This gives users the impression all programs are executed simultaneously. This is called system timeshare.
Some call pseudo-parallel this very rapid switching of a processor program to another, to differentiate it from true parallelism that occurs at the equipment when the processor works in conjunction with some of input-output devices.
Abstraction of the course
Conceptually, each process has its own virtual processor. Of course, the real processor switches between multiple processes. But to understand the system, it is pre-preferable to think of a set of processes that are running in (pseudo) parallel rather that the allocation of the processor between different processes. This rapid switching is applied multi-programming.
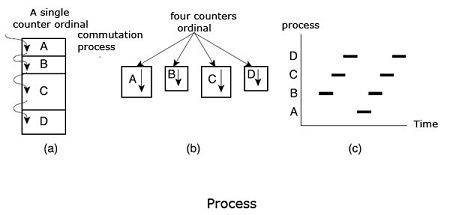
Figure 1 shows four processes running simultaneously. Figure (b) shows an abstraction of this situation. The four programs become four independent processes, each with its own flow control (that is to say, their program counter). In Figure (c), it can be seen that, over a time interval sufficiently big, all processes have improved, but at a certain moment, there is only one process assets.
Environment Variables
As we have already said, the program is insufficient data to determine a process. It should indicate a number of environment variables: the files on which it operates, which is the program counter, etc. These environment variables are necessary for two reasons:
The first is that two processes can use the same code (two Emacs windows example), but the affected files may be different; the program counter does not be in the same place.
The second is due to the multi-tasking nature processed by pseudo-parallelism. Periodically, the operating system decides to stop a running process to start executing another process. When this process is suspended temporarily, it must be able to find later the exact state it was in time of suspension. This requires that all the information he needs to be saved somewhere for her on hold. If it has, for example, several open files, positions in these files should be stored.
The list of environment variables depends on the operating system in question, even its version. It is located in the descriptor of the process.
Memory space of a process
In many operating systems, each process has its own memory space, not available to other processes. We speak of the address space of the process.
Affect the treatment duration
Since the processor switches between processes, speed of execution of a process is not uniform and is likely to change if the same processes are executed again. So do not make the process any presumption on factor time.
Consider the case of an input-output process which starts the engine of a drive diskettes, runs 1000 times a loop for the speed of the disk is stabilized, then requests reading the first record. If the processor has also been allocated to another process during execution of the loop, the input-output process may be reactivated too late, that is to say, after the passage of the first record before the playhead. When a process needs to measure time accurately, that is to say, when some events need to happen every few milliseconds, take special measures to make sure. It then uses timers, as the see.
However, most processes are not affected by the multi-processor programming and by the differences in execution speed between them.
Multi-user Systems
A multi-user system is able to perform so (pseudo-) and competing Separate applications belonging to several users.
Competing means that applications can be active at the same time and hassle access to different resources such as CPU, memory, hard drives …Independent means that each application can perform their work without worrying what are the applications of other users.
A multi-user system is necessarily multi-tasking, but the converse is false: the MS-DOS operating system is single-user and single-task; Mac OS 6.1 and Windows 3.1 is single user but multitasking; UNIX and Windows NT are multi-user.
Mise in place
As for multi-tasking systems, multi-use is emulated by assigning period time to each user. Naturally, the fact to switch from one application to another slows each and affects the response time perceived by the users.
Associated mechanisms
When they allow multi-use, the operating system must provide a number of mechanisms:
– An authentication mechanism for verifying the identity of the user;
– A protection mechanism against erroneous user programs that could block other applications running on the system, or malicious, which could disrupt or spy on the activities of other users;
– An accounting mechanism to limit the amount of resources allocated to each user.
Users
In a multi-user system, each user has a private area on the machine: generally, it has a certain quota of disk space to store its files, receives private e-mails, etc. The operating system must ensure that the private party space a user can not be visible to the owner. He must, in particular, ensure that no user can not use an application of the system the purpose of violating the private area of another user.
Each user is identified by a unique number, called the ID of the user, or UID (User Identifier). In general, only a limited number of persons allowed using a computer system. When one of these users starts a work session, the operating system asks for a user name and password. If the user does not respond with valid information, access is denied.
User Group
To selectively share materials with others, each user can be member of one or multiple user groups. A group is also identified by a unique number called the group ID (GID for Group Identifier). For example, each file is associated with one and only one group. On UNIX, it is possible for example, to limit access in reading and writing in the sole possessor of a file, read the group, and to deny them access to other users.
Super user
A multi-user operating system provides a special user called root or supervisor (root in English). The system administrator must log time super user to manage user accounts and perform tasks maintenance such as backups and program updates. The super user can do almost anything in that the operating system never applies the protection mechanisms they do on other users, called ordinary users. The root can, in particular, access all files in the system and interfere with the activity of any running process running. It can not, however, access to the input-output ports that have not been provided by the kernel, as we shall see.
 Dinesh Thakur holds an B.C.A, MCDBA, MCSD certifications. Dinesh authors the hugely popular
Dinesh Thakur holds an B.C.A, MCDBA, MCSD certifications. Dinesh authors the hugely popular