In the late 1960s, the US Department of Defense decides to make an extensive network from many small networks, all different, which begin to abound everywhere in North America. We had to find a way for these networks to coexist and give them outdoor visibility, the same for all users. Hence, InterNetwork (interline), abbreviated as the Internet, data this network of networks.
The Internet architecture is based on a simple idea: ask all networks to carry a single packet type, a specific format, the IP protocol. Besides, this IP packet must have an address defined with sufficient generality to identify each computer and terminals scattered throughout the world. This architecture is illustrated in Figure.
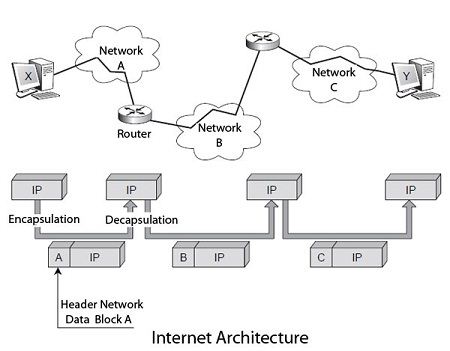
The user who wishes to make on this internetwork must store its data in IP packets delivered to the first network to cross. This first network encapsulates the IP packet in its packet structure, package A, which circulates in this form until an exit door, where it is decapsulated to retrieve the IP packet. The IP address is examined to locate, thanks to a routing algorithm, the following network to cross, and so on until arriving at the destination terminal.
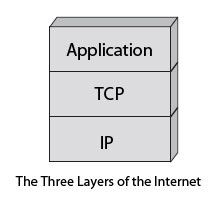
To complete the IP, the US Defense added the TCP protocol; specify the nature of the interface with the user. This protocol further determines how to transform a stream of bytes in an IP packet while ensuring the quality of transport of this IP packet. Both protocols, assembled under the TCP / IP abbreviation, are in the form of a layered architecture. They correspond to the packet level and message-level reference model.
The Internet model completed with a third layer called the application level, which includes different protocols for building Internet services. Email (SMTP), file transfer (FTP), the transfer of hypermedia pages, transfer of distributed databases (World Wide Web), etc., are some of these services. The figure shows the three layers of Internet architecture.
IP packets are independent of each other and are individually routed in the network by interconnecting devices, subnets, routers. The quality of service offered by IP is minimal and provides no detection of lost or possibility of error recovery packages.
TCP combines the functionality of the message-level reference model. It is a fairly complex protocol with many options for solving all packet loss problems in the lower levels. In particular, a lost fragment can be recovered by retransmission on the stream of bytes. TCP uses a connection-oriented mode.
The flexibility of the Internet architecture can sometimes be a default. The extent that global optimization of the network is carried out by sub-network subnet, by a succession of local optimizations. It does not allow a homogeneous function in different subnets traversed. Another essential feature of this architecture is to place the entire control system, to say, intelligence and control of the network, in the terminal machine, leaving virtually nothing in the network, at least in the current version, IPv4, the IP protocol. The control intelligence is in the TCP software on the PC connected to the network.
It is the TCP protocol that takes care of sending more or fewer packets according to network load. Precise control window the maximum number of unacknowledged fragments that may be issued. The TCP window control increases or decreases the traffic following the time required to complete a round trip. Over this time increases, Considering the more congested network, the transmission rate must decrease to counter saturation. In return, the infrastructure cost is meagre; no intelligence is not in the network. The service provided by the network of networks corresponds to a quality called the best effort, which means that the network does its best to carry the traffic. In other words, the service quality is not assured.
The new generation of IP, IPv6, introduces new features that make the network nodes smarter. The new generation of routers comes with QoS management algorithms, which allow them to provide transportation that can meet time constraints or packet loss. We expect the arrival of IPv6 for ten years, but it’s still IPv4 IP that governs the world. Because every new need is achievable with IPv6, IPv4 has been able to find the algorithms needed to do as well.
In IPv4, each new customer is treated the same way as those already connected, with resources being distributed equitably among all users. The resource allocation policies of telecom operator’s networks are different since, on these networks, a customer who already has a certain quality of service does not suffer any penalty because of the arrival of a new customer. As discussed, the now advocated solution in the Internet environment is to encourage customers with real-time requirements, using appropriate protocols, using priority levels.
The IP protocol for thirty years but remained almost confidential for twenty years before taking off, unless its properties resulted from the failure of the protocols directly related to the reference model, too many and often incompatible. The IP world growth comes from the simplicity of its protocol, with very few options, and it’s free.
 Dinesh Thakur holds an B.C.A, MCDBA, MCSD certifications. Dinesh authors the hugely popular
Dinesh Thakur holds an B.C.A, MCDBA, MCSD certifications. Dinesh authors the hugely popular