FDDI stands for Fiber Distributed Data Interface. It is a high-speed, high-bandwidth network based on optical transmissions. It is most often used as a network backbone, for connecting high-end computers (mainframes, minicomputers, and peripherals), and for LANs connecting high-performance engineering, graphics, and other workstations that demand a rapid transfer of large amounts of data. It can transport data at a rate of 100 Megabits per second and can support up to 500 stations on a single network. FDDI was designed to run through fiber cables, transmitting light pulses to convey information between stations, but it can also run on copper using electrical signals. It is relatively expensive to implement, although the mixing of fiber-optic with copper cabling can hold down the cost.
FDDI is highly reliable because FDDI networks consist of two counter-rotating rings. A secondary ring provides an alternate data path in the event a fault occurring on the primary ring. FDDI stations incorporate this secondary ring into the data path to route traffic around the fault. FDDI based on a ring topology with token passing. It is an advanced technology, in the form of the token ring over optical fiber. FDDI developed for two primary reasons: to support and help extend the capabilities of older LANs, such as Ethernet and Token Ring, and to provide a reliable infrastructure for businesses, moving even mission-critical applications to networks.
We’ll be covering the following topics in this tutorial:
History of FDDI
FDDI is an ANSI (American National Standards Institute) networking standard, and ANSI began working on the FDDI -Standard in 1982. The FDDI specification released in 1986. ANSI chose the ring as network topology for FDDI. The most critical elements of FDDI were defined in 1989 (as ANSI X3T9.5) and parts have been adopted by the ISO (International Standards Organizations) as well. FDDI also considered as a successor of IEEE 802.5 standards (token ring). FDDI has higher capacity than token rings. FDOI comprises two bottom layers in the ISO’s Open System Interconnection (OSI) model namely, Layer 1 (Physical layer) and Layer 2 (Data Link layer). Physical layers are PMD, PHY.
The current version of the FDDI standard defines in ANSI X3T12. To ensure interoperability, the vendors tested their products at the ANTC (Advanced Network Test Center) and EANTC (European ANTC). It ensures that many vendors support FODI with their products. Products from different vendors can easily mix in an FDDI network. It is the most significant advantage of FDDI.
Although FDDI is not really a WAN technology (its ring are limited to a maximum length of 100 kilometers or 62 miles), the ground it can cover does make it suitable for use as a backbone, connecting a number of smaller LANs, and it can provide the core of a network as extensive as a Metropolitan Area Network (MAN). In that sense, FDDI is more than LAN but less than WAN. Also, because FDDI transfers information extremely quickly (l00 Mbps), it is often used to connect high-end devices such as mainframes, minicomputers, and peripherals, or to connect high-performance devices within a LAN. Engineering or video or graphics workstations, for instance, benefit from FODI because they need much bandwidth, to transfer large amounts of data at satisfactorily high steeds. FDDI can easily be incorporated into existing networks because it works even with other network topologies (due to the LLC protocol that is also used by Ethernet and Token Ring).
FDDI Features
FDDI is an efficient network topology, regarding fault-tolerance and integrated network management functions. With its deterministic access methods, FDDI guarantees high aggregated throughput rates, even in large and high traffic networks. FDDI can be added easily to existing network topologies (such as Ethernet and Token Ring) as a strong backbone to eliminate severe network bottlenecks in existing LANs.
FDDI offers the following features:
• High transmission rates (100 Mbps) and bandwidth
• Real throughput rate (20 stations expected) of approx. 95 Mbps
• Large extensions (max. 100 km)
• Great node-to-node distance (2km using multimode fiber, 40 km using single mode fiber)
• Available for both fiber and copper media
• Easier to maintain
• Compatible to standards-based components and various operating systems.
Cabling Requirement
Optical fiber is the transmission medium of FDDI networks-but copper media also can be used for standard office connections offering the same transmission rates. In contrast to copper media, fiber provides the best possible protection against physical network tapping and offers immunity to electromagnetic interference. As its name indicates, FDDI developed around the idea of using optical fiber cable. It is, in fact, the type of cable used, especially when the high-speed transmission needed over relatively long distances (2000 to 10,000 meters, or roughly 1 to 6 miles). However, over shorter distances (about 100 meters, or 330 feet), FDDI can also be implemented on less expensive copper cable.
In all, FDDI supports four different types of cable:
• Multimode fiber optic cable: This type of cable can be used over a maximum of 2000 meters and uses LED as a light source.
• Single mode fiber optic cable: This can be used over a maximum of 10,000metres or more and uses lasers as a light source. Single mode cable is thinner at the core than multimode, but it provides higher bandwidth because of the way the light impulse travels through the cable.
• Unshielded twisted-pair copper wiring: This cable contains eight wires, and as the next category, can be used over distances up to 30 meters.
• Shielded twisted-pair copper wiring: This is a shielded cable that contains two pairs of twisted wires, with each pair also shielded.
The Fiber PMD (Physical Medium Dependent)
PMD defines specifications for the physical layer of a network standard, namely, the media and interface connectors used. As FDDI supports both fiber and copper media, two separate specifications are defined. They are the Fiber PMD (for optical fiber media) and TP-PMD (for copper media, specifically for twisted-pair). Other two significant PMDs are SMF-PMD (Single Mode Fiber-PMD), defines the demands on single mode fibers permitting distances of 40 to 60 km (in contrast to multimode fibers permitting distances of maximum 2 km).
LCF-PMD (Low-Cost Fiber-PMD) was developed to get a low-price, fiber-based alternative with restrictions to the maximum distance between nodes at the same time. The duplex SC connector introduced by LCF-PMD mainly adopted by the full power budget version of Fiber PMD.
The Fiber PMD-ANSI X3T9.5/48-48 describes the physical layer that uses fiber and optical components. It defines the following characteristics and parameters of the optical fiber cables allowed for FDDI.
• The wavelength of light (nominal wavelength is 1,300 nm)
• Attenuation and bandwidth
• Maximum bit-error rate
• Dispersion of optical media
• The numerical aperture (sine’s of aperture angle for total internal reflection, the nominal aperture is 0.275)
• Intensity of light
• The jitter of the pulse
• Allowed power between two stations
62.5/125 and 85/125 micrometers graded index fibers defined as transmission media.
50/125 and 100/140 micrometers graded index fibers are also accepted.
PHY (Physical Layer Protocol)
The PHY document describes the physical processes on the medium (example data encoding). It defines:
• Data encoding/ decoding.
• Clock synchronization (as FDDI rings can grow rather big, there is no central clock frequency).
• TVX (Valid Transmission Time).
• Line states (Quiet – no signal on the line, Idle – normal line state, Halt and Master use when transmitting configuration data).
• Control symbols (Start delimiter send when the data transmission starts and ending delimiter tells when the FDDI frame should terminate.
• Data symbols (hexadecimal symbols 0 to F).
• Violation symbols (example the symbol v means that an illegal signal is on the line).
The maximum number of Phys per FDDI ring is 1000. A Dual Attachment Station (OAS) has two PHYs connected directly to the double ring, whereas a SAS (Single Attached Station) has an additional PHY in the concentrator. As each station needs two PHYs, the network can accommodate a maximum of 500 stations.
MAC (Medium Access Control) Layer
The MAC (Medium Access Control) layer of the FDDI specified within the data link layer. It uses the token passing method as medium access method and allows each station accessing the ring in precisely defined intervals. The IEEE 802.2 standard applied in the LLC (Logical Link Control) layer. Due to the LLC protocol, FDDI smoothly integrates network topologies such as Ethernet (IEEE 802.3) and Token Ring (IEEE 802.5).
The MAC layer comprises address identification generating and checking the FCS (Frame Check Sequence) checksum. Beside it specifies transmitting, repeating, and deleting MAC frames just as providing MAC services to the LLC layer. Additionally, the MAC layer specifies how to handle synchronous and asynchronous data traffic. The critical difference between the IEEE 802.5 protocol and the FDDI are as follows.
• A station is waiting for a token abort the token transmission in FDDI. However, in IEEE 802.5 (Token ring) protocol, it naturally complements the selected bit in the token. It is due to the high data rate of FDDI.
• An FDDI station releases the token as soon as the last frame is released (early release in IEEE
802.5), as waiting for the transmitted frame (standard IEEE 802.5) to return inefficient in a high-speed environment.
SMT (Station Management)
Station management provides the control necessary at the node level to manage the functions of various FDDI layers. Individual network control and safety mechanisms used for controlling and managing activities on the ring and the connection of every station. Furthermore, it allows reconfiguring the ring in case of malfunction or line-disruption. The SMT function permanently monitors the FDDI ring. It coordinates the configuration during network start-up and produces status accounts on the ring’s and station’s states. The SMT manages the Phys, MACs, and PMDs of each station. Besides, SMT is responsible for counters, parameters, and statistics.
The functionality of the SMT can divide into CMT (Connection management) and RMT (ring management). The CMT again is divided into:
ECM (Entity Coordination Management): Coordinating the activities of all PHYs and controlling the optional optical bypass function.
PCM (Physical Connection Management): Inserting and removing stations, initializing, and coordinating physical connections between local and neighboring ports.
CFM (Configuration Management): Responsible for configuring MAC and PHY of an FDDI station.
Further, each port of an FDDI station has a CEM (Configuration Element Management).
The RMT manages the MAC components, such as changing a MAC address to a unique address and removing a MAC with a duplicate address from the ring. Further, the RMT monitors the FDDI ring and manages adequate procedures in case of ring disruption.
FDDI Topology
The FDDI network topology may view at two distinct levels.
• The physical level
• The logical level
Physical topology describes the arrangement and interconnection of nodes with physical connections. The logical topology describes the paths through the network between MAC entities. An FDDI network forms one of the two following physical topologies:
• A dual ring of trees.
• A subset of a dual ring of trees.
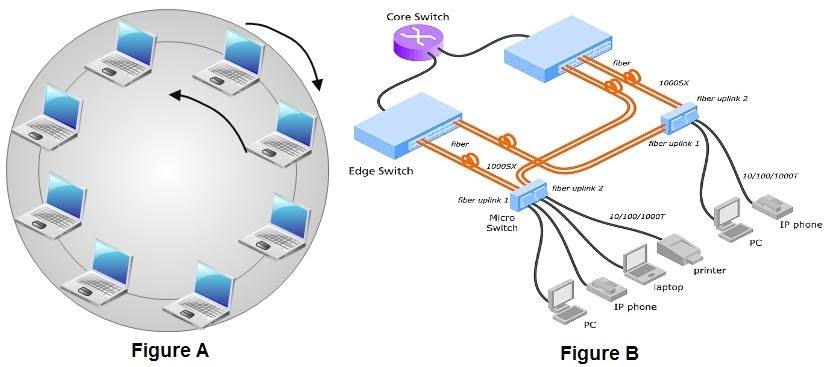
FDDI uses a dual ring topology. The dual ring topology uses two counter-rotating rings known as the primary and secondary ring. The primary ring is similar to the main ring path in token-ring terminology. The secondary ring is similar to the backup ring path of a token-ring. Each ring consists of a single fiber path, which is equivalent to a pair of copper conductors. FDDI topology permits many attachment units (stations, concentrators, and bridges) to attach in various ways. From a wiring point of view, FDDI is similar to a fiber optic token-ring network; however, there are differences between the token-ring and FDDI techniques. A device can be attached directly to the ring without requiring a concentrator such as the Multi-station Access Unit (MAU) on a token-ring. A device can be attached to either one or both of the primary and secondary rings.
Station Types
To differentiate between devices that attach to one ring or both rings, FDDI defines two classes of devices. A Class A device attaches to both the rings directly. It may be a station and is called a Class A station or a Dual Attachment Station (OAS). It can also be a concentrator, and in this case, it is called a Dual Attachment Concentrator (OAC).
A Class B device is a station attaches to only one of the rings, directly or through a concentrator. Concentrators are active devices that act as wiring hubs. A Class B station called as Single Attachment Station (SAS). It can also be a concentrator, and it is called a Single Attachment Concentrator (SAC). During regular ring operation, the primary ring is active while the secondary ring is idle. In the wake of a failure on the primary ring, the secondary ring become active when a class A station or a Dual Attachment Concentrator wraps the primary ring to the secondary ring, establishing a single ring. This functionality is mandatory to maintain the reliability of the LAN. Figure(a) illustrates the dual ring topology.
The FDDI dual ring configuration consists of Dual Attachment Stations (OAS). A dual attached station on the ring has at least two ports, an A port, where the primary ring comes in, and the secondary ring goes out, and a B port where the secondary ring comes in, and the primary goes out. Each station has both ports (A and B) attached to the rings. The cabling between the stations has to be all fiber or shielded twisted-pair (STP).
Dual Homing
To attain better fault tolerant, a particular topology known as dual homing use. A concentrator that is not part of the main ring may be dual attached via one or two other concentrators to provide higher availability. When connected in this manner, a concentrator described as a Dual Homing Concentrator (DHC). Similarly, a Dual Attachment Station can be connected to one or two concentrators using both A and B ports to provide high availability. The station connected in this manner is considered a Dual Homing Station (DHS). In both cases, only port B is active, and the connection to port A remains in standby mode. If the connection to port B fails, port A become active without any impact on the users of the Dual-Homed station or concentrator. Figure (b) illustrates the dual homing technique.
Operation of FDDI
FDDI topology and operation are similar to Token Ring. The sequence in which stations gain access to the medium is predetermined. A station generates a particular bit sequence called a Token that controls the right to transmit. The Token is continually passed around the network from one node to the next. Each station has the chance to transmit data when a token passes. A station can decide how many frames it transmits using an algorithm that permits bandwidth allocation. FDDI also allows a station to transmit many frames without releasing the token. When a station has some data to send, it captures the token, sends the information in the form of well-formatted FDDI frames, and then releases the token. The header of these frames includes the address of the station(s) that copy the frame. All nodes read the frame as it passes around the ring to determine if they are the recipients of the frame. If they are, they extract the data and retransmit the frame to the next station on the ring. When the frame returns to the originating station, the originating station removes the frame. The token-access control scheme thus allows all stations to share the network bandwidth in an orderly and efficient manner.
Generally, in an FDDI network, one ring (known as the primary ring) carries the tokens and data frames, and the secondary ring remains idle and uses as a backup for fault tolerance or insurance. Because the secondary ring is available if needed, whenever a nonfunctioning node causes a break in the primary ring, traffic ‘Q’ a “wrap” around the problem causing node and continue to carrying data, only in the opposite direction and on the secondary ring. That way, even if a node goes down, the network continues to function. Of course, it is also possible for two nodes to fail. When this happens, the wrap at both locations effectively segments the one ring into two separate, non-communicating rings. To avoid this potentially dangerous problem, FDDI networks can rely on concentrators. These concentrators resemble hubs or MAU in that multiple nodes plugs into them. They are also able to isolate any failed nodes while keeping the network traffic flowing. Sometimes, both rings use for data transfer. In this case, the data travels in one direction (clockwise) on one ring and in the other direction (counterclockwise) on the other ring. Using both rings to carry data makes the number of frames twice that of the standard rate. Hence, the speed of the network can double, from 100 Mbps to 200 Mbps.
Frame Format
An FDDI frame is very similar to that defined by the traditional token ring, but there are only eight fields. The Token and frame format for the FDDI shown in Figure (a) and (b), respectively. The Control token structure is very much similar to the Token ring case.
Eight fields make up the FDDI frame. They are:
As you can see, the data token in FDDI is very similar to the token ring data token we saw earlier. The access control byte or octet is missing.
Start Delimiter: The Start Delimiter of a token is an indicator of the start of the token. It consists of the symbols ‘J’ and ‘K,’ and these symbols not be seen anywhere else but at the start of a frame or token.
Frame Control: The frame control gives information about the type of the token. A value of hexadecimal 80 in the frame control field denotes a Non-restricted Token, while a frame control of hexadecimal CO is a restricted token.
Destination Address: It is a 12-symbol code that indicates the identity of the station to which the frame is to send. Each station has a unique 12-symbol address that identifies it. When a station receives a frame, it compares the OA of that frame to its address if the two match, the station copy the contents of the frame into its buffers.
The destination address can be an individual address or a group address that depends on its first. If the first bit set to (1), the address is a group address. If it set to (0), the address is an individual address. Group addresses can be used to address a frame to multiple destination stations. A broadcast address is a particular type of group address, which applies to all of the stations on the network.
Source Address: This field indicates the address of the station that created the frame. In FDDI, when a station creates a frame, the frame is passed from one station to the next until it returns to the originating station. The originating station removes the frame from the physical medium.
Data: This field carries the actual information to be conveyed. Every frame is mostly built around this field and is merely a mechanism for getting the info from one station to another. The type of information contained in the data field determined from the Frame Control of the field of the frame.
Cyclic Redundancy Check (CRC): CRC is used to verify whether the incoming frame contains any bit errors. The FCS is generated by the station that sourced the frame, using the bits of the FC, OA, SA, DATA and CRC fields. The CRC generated such that, should any of the bits in those fields be altered, then the receiving station notice that there is a problem and discard the frame.
Ending Delimiter: This field consists of two ‘T’ symbols. These ‘T’ symbols indicate that the token is complete. Any data sequence that does not end with these ‘T’ symbols is not considered a token.
Frame Status: The Frame Status consists of three indicators, which may have one of two values set and reset. The three indicators are Error (JE’), Address recognized (or Acknowledge) (‘N), and Copy (‘C).
FDDI Token Passing
Token passing on an FDDI network works much the way it does on a Token Ring network, that is, nodes pass a token around the ring, and only the node with the token is allowed to transmit a frame. There is a twist to this. However, that is related to FDDI fault tolerance. When a node on the ring detects a problem, it is not idle. Instead; it generates a control frame known as a beacon and sends it on to the network. As neighboring nodes detect the beacon, they too begin to transmit beacons, and so it goes around the ring. When the node that started the process, eventually receives its beacon back usually after the network has switched to the secondary ring, it then assumes that the problem has been isolated or resolved, generates a new token, and starts the ball rolling once again.
Structure of a FDDI Network
An FDDI network, as already mentioned, cannot include rings longer than 100 kilometers apart. Another restriction on an FDDI network is that it cannot support more than SOD (nodes per ring. Although the overall network topology must conform to a logical ring, the network does not have to look like a circle. It can include stars connected to hubs or concentrators, and it can even include trees collections of hubs connected in a hierarchy. As long as the stars and trees connect in a logical ring, the FDDI network does not face any problem.
Existing networks like Ethernet and Token Ring networks can integrate via workgroup switches or routers into an FDDI backbone. Fileservers should be connected directly to the FDDI backbone to reduce data load and to provide reasonable access time for the user. The availability of FDDI adapters for twisted-pair allows smooth migration of existing cabling to FOOL High-End PC workstations with applications like CAD, CIM, CAM, DTP, or image processing can be connected directly to the FDDI ring via FDDI network interface cards and concentrators.
 Dinesh Thakur holds an B.C.A, MCDBA, MCSD certifications. Dinesh authors the hugely popular
Dinesh Thakur holds an B.C.A, MCDBA, MCSD certifications. Dinesh authors the hugely popular